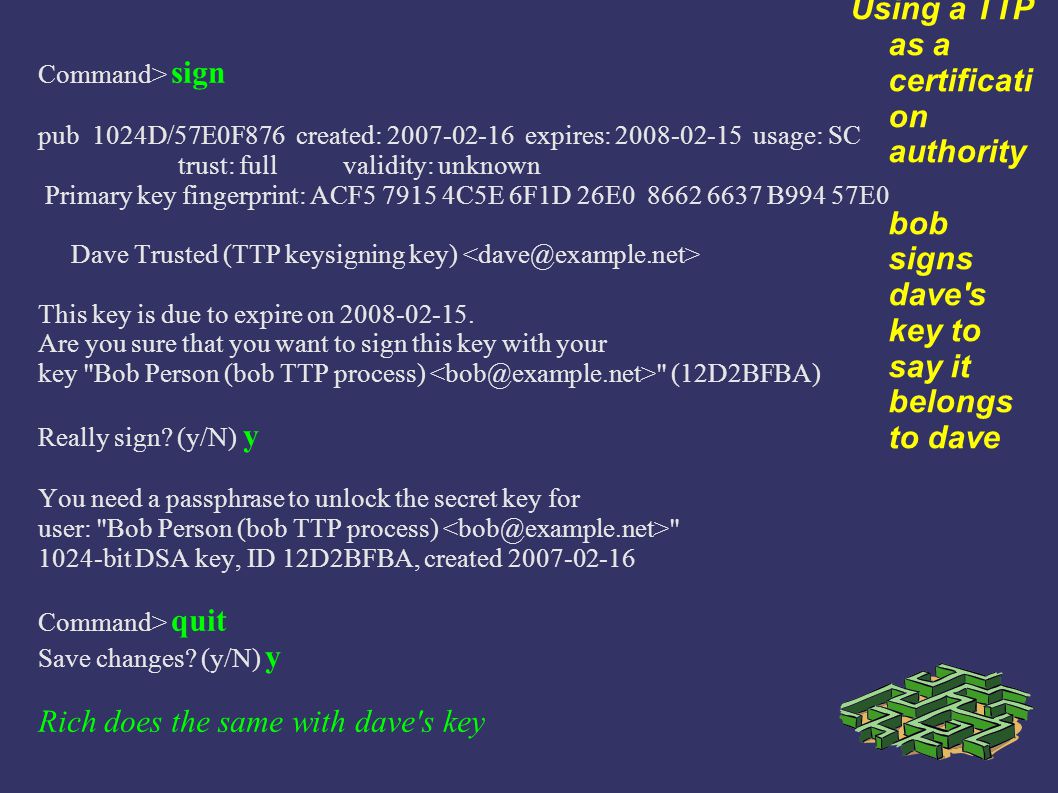
Using GPG - the GNU Privacy Guard Why does a security professional need this skill ? 3 GPG HOWTO's Use by checking Correspondents' Keys Directly Using. - ppt download
2021 Women's Conference USSSA Update after the Conference Championship! - www.softballcenter.comwww.softballcenter.com
![PDF] A Hierarchical Trusted Thir d-Party System for Secure Peer-to-Peer Transactions | Semantic Scholar PDF] A Hierarchical Trusted Thir d-Party System for Secure Peer-to-Peer Transactions | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/f5e9dd671605683559b5d880d9ac04a78d3fd02b/16-Table1-1.png)